How IoT Affects Your Company’s Cybersecurity and What To Do About It

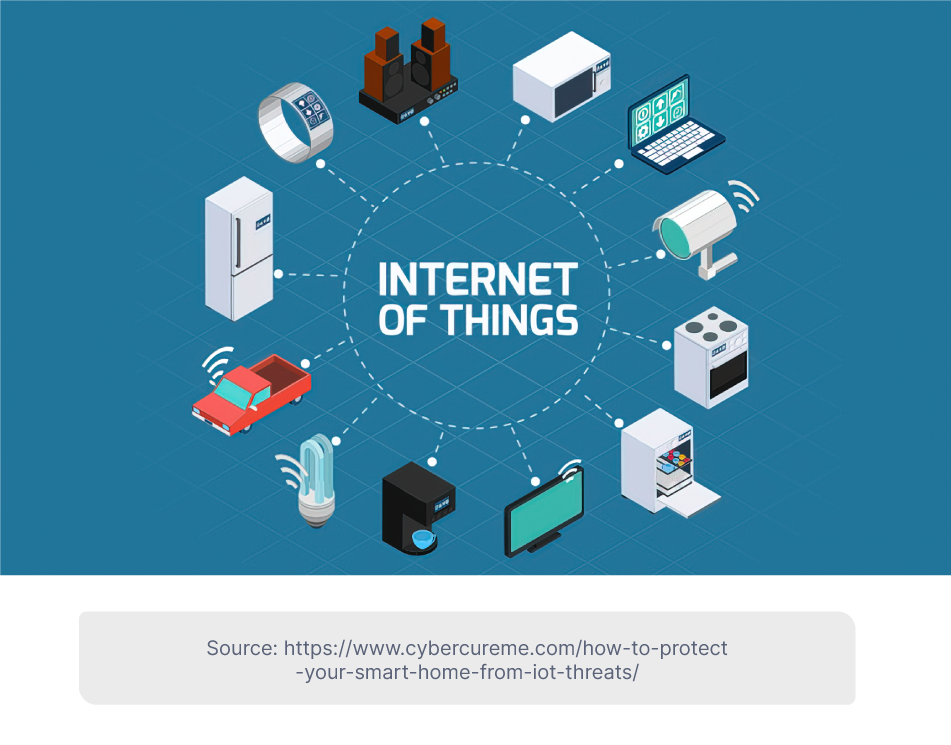
We’ve heard a lot about how the ‘Internet of Things’ (IoT) is going to change all aspects of our daily lives. The IoT is a system of inter-connected objects that can communicate over the internet without the need for human intervention. In practice, this means our watches, fridges, cars and supermarkets are embedded with networking and computing capabilities. These everyday objects connect to the web, collect and share data, and act on information to better cater to our needs.
There’s little doubt that the IoT is going to be one of the key tech trends over the next decade. According to IoT Analytics, the number of connected IoT devices worldwide is expected to reach 27 billion by 2025, more than double the estimated 12.9 billion in 2021. A recent McKinsey report estimates that the IoT could unlock $5.5 trillion to $12.6 trillion in value globally by 2030. But such rapid growth doesn’t come without problems. And chief among them right now is IoT cybersecurity.
IoT & Cybersecurity
Cybersecurity is a major risk for all businesses as more operations and data are moved online. Research shows that average weekly corporate cyber attacks rose by 50% during 2021. The latest annual Allianz Risk Barometer survey found that ‘cyber incidents’ are the main concern for companies in 2022, particularly ransomware attacks and data breaches.
The IoT adds several new dimensions to this cybersecurity threat. Why? Firstly, because each new device that connects to the internet is a potential entry point for cyber criminals. As more of the everyday objects around us come online, the attack surface of our private networks expands. It’s no longer just our phones and laptops that are potentially vulnerable to cyber attacks, but our speakers, doorbells and thermostats. At a larger scale, the rapid growth of the IoT implies an ever-expanding network of devices that could be hacked.
-png.png)
Secondly, IoT devices are often an easier target for malicious actors. Our computers can be protected with sophisticated cybersecurity software that is regularly updated to defend against new threats. But many new IoT devices have limited processing capabilities, making it more difficult to install firewalls, antivirus software or security patches. A recent report found that nearly half of internet-connected devices used in hospitals are vulnerable to hacks.
Finally, the expansion of the IoT leaves us all increasingly dependent on connected devices. This means any successful hack could be more disruptive and costly, whether at a personal, businesses or societal level. Consider all the sensitive data that could be accessed if financial or health IoT systems are compromised. Or the damage that hackers could do if they gain control of transport or security systems in smart cities.
How can businesses manage IoT cybersecurity risks?
Given the risks above, companies rolling out IoT systems and devices need to make cybersecurity an integral part of their business strategy. Protection against cyber attacks will be far more effective if security measures are baked into design and procedures rather than added on later as an afterthought. Here are five things your company can do to enhance IoT cybersecurity.
- Understand your vulnerabilities: The first defense against cyber attacks is prevention. An IT team needs to know what the organization’s attack surface is and identify any vulnerabilities in end-point devices both on-site and remote. The IoT sensors and networks connecting all these devices must also be continuously assessed for any security weaknesses. Another task is to be aware of the most common cyber attacks that target IoT systems, so that you can defend the right areas. From a privacy perspective it’s also important to know how the IoT devices you use collect, store and share data.
-png.png)
- Ensure proper password management: Everyone in a business organization needs to be using secure passwords. This is especially important as remote working becomes more common and as more devices are integrated into the organization’s IoT systems. Access to IoT devices should be controlled with secure processes such as Single Sign-On (SSO) and Multi-Factor Authentication (MFA). Devices that use default passwords or can’t be properly secured shouldn’t be integrated into the wider network.
- Make use of existing frameworks and technology: Businesses should draw from existing guidelines and standards when developing a comprehensive IoT cybersecurity strategy. For example, the National Institute of Standards and Technology (NIST) has a cybersecurity for the IoT program that aims to engage global stakeholders to develop effective tools and best practices. Companies can also integrate machine learning (ML) and artificial intelligence (AI) tools to improve how they monitor and respond to cybersecurity threats.
- Compartmentalize IoT systems: You can never have 100% guaranteed protection, so it’s vital to have effective containment measures in place to limit the impact of a successful cyber attack on your business. One approach is to use loosely-coupled IoT systems, so that if one device is compromised it won’t necessarily spread to all business operations. Using multi-layered security measures and tools can act as internal digital “fences” around certain devices or networks, mitigating the impact of a hack.
- Minimize third-party IoT risk: Some things are beyond the direct control of management, but it’s still prudent to take measures to mitigate external IoT risks. This means conducting proper due diligence on third-party producers and vendors of IoT devices, ensuring these parties understand IoT cybersecurity and take the risks seriously. These third-party vendors can also play an important role in ensuring IoT devices can be updated to protect against new and emerging threats.
The IoT brings numerous potential benefits for individuals, businesses and societies, but these can only be realized if we collectively work to limit the opportunities for cyber criminals. Beyond adopting best practices today, companies should be open to discussion and debate about how to protect against IoT cybersecurity threats in the future.
With over +16 years of experience in the technology and software industry and +12 of those years at Jobsity, Santi has performed a variety of roles including UX/UI web designer, senior front-end developer, technical project manager, and account manager. Wearing all of these hats has provided him with a wide range of expertise and the ability to manage teams, create solutions, and understand industry needs. At present, he runs the Operations Department at Jobsity, creating a high-level strategy for the company's success and leading a team of more than 400 professionals in their work on major projects.